]
] Journal of Computer Security, vol. 27, issue 5, Elsevier, pp. 521-546, 09/2019.
European Symposium on Research in Computer Security (ESORICS 2018), vol. 11098, Springer, pp. 555-574, 08/2018. DOI
Abstract
Advanced persistent threats pose a serious issue for modern industrial environments, due to their targeted and complex attack vectors that are difficult to detect. This is especially severe in critical infrastructures that are accelerating the integration of IT technologies. It is then essential to further develop effective monitoring and response systems that ensure the continuity of business to face the arising set of cyber-security threats. In this paper, we study the practical applicability of a novel technique based on opinion dynamics, that permits to trace the attack throughout all its stages along the network by correlating different anomalies measured over time, thereby taking the persistence of threats and the criticality of resources into consideration. The resulting information is of essential importance to monitor the overall health of the control system and correspondingly deploy accurate response procedures.

International Journal of Critical Infrastructure Protection (IJCIP), vol. 8, Elsevier Science, pp. 53–66, 01/2015. DOI
Abstract
Critical infrastructures play a vital role in supporting modern society. The reliability, performance, continuous operation, safety, maintenance and protection of critical infrastructures are national priorities for countries around the world. This paper explores the vulnerabilities and threats facing modern critical infrastructures with special emphasis on industrial control systems, and describes a number of protection measures. The paper also discusses some of the challenging areas related to critical infrastructure protection such as governance and security management, secure network architectures, self-healing, modeling and simulation, wide-area situational awareness, forensics and learning, and trust management and privacy.
IEEE Computer, vol. 46, no. 10, IEEE Computer Society, pp. 74 - 83, 2013. DOI
Abstract
Information systems, networks, and technologies have become an integral part of modern critical control systems that manage many of today’s critical infrastructures. The continuous operation, maintenance, and protection of critical infrastructures have become a high national priority for governments around the world because our society heavily depends on them for most of our daily activities (travel, power usage, banking transactions, telecommunications, etc) and safety. It is therefore critical that these infrastructures have to be protected from potential accidental incidents or cyberattacks. We present the fundamental architectural components of critical control systems which manage most critical infrastructures. We identify some of the vulnerabilities and threats to modern critical control systems followed by protection solutions that can be deployed to mitigate attacks exploiting these vulnerabilities.
21st International Conference on Computer Communications and Networks (ICCCN), IEEE Computer Society, pp. 1-5, Jul 2012. DOI
Abstract
Migration to an electronically controlled electrical grid to transmit, distribute, and deliver power to consumers has helped enhance the reliability and efficiency of conventional electricity systems. At the same time, this digitally enabled technology called the Smart Grid has brought new challenges to businesses and consumers alike. A key component of such a grid is the smart-metering technology, which is used to collect energy consumption data from homes and transmitting it back to power distributors. A crucial concern is the privacy related to the collection and use of energy consumption data. We present an analysis of Smart Grid privacy issues and discuss recently proposed solutions that can protect the privacy of Smart Grid users.
Wireless Personal Communications, vol. 73, Springer, pp. 23-50, Nov 2013, 2012. DOI
Abstract
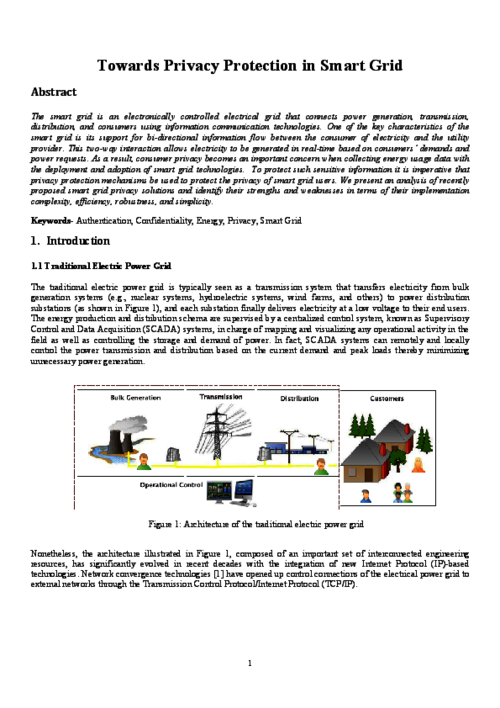
The smart grid is an electronically controlled electrical grid that connects power generation, transmission, distribution, and consumers using information communication technologies. One of the key characteristics of the smart grid is its support for bi-directional information flow between the consumer of electricity and the utility provider. This two-way interaction allows electricity to be generated in real-time based on consumers’ demands and power requests. As a result, consumer privacy becomes an important concern when collecting energy usage data with the deployment and adoption of smart grid technologies. To protect such sensitive information it is imperative that privacy protection mechanisms be used to protect the privacy of smart grid users. We present an analysis of recently proposed smart grid privacy solutions and identify their strengths and weaknesses in terms of their implementation complexity, efficiency, robustness, and simplicity.
Concurrency and Computation Practice & Experience, vol. 23, no. 12, John Wiley & Sons, Inc., pp. 1414-1430, Aug 2011. DOI
Abstract
Energy distribution systems are becoming increasingly widespread in today’s society. One of the elements that is used to monitor and control these systems are the SCADA (Supervisory Control and Data Acquisition) systems. In particular, these control systems and their complexities, together with the emerging use of the Internet and wireless technologies, bring new challenges that must be carefully considered. Examples of such challenges are the particular bene¯ts of the integration of those new technologies, and also the e®ects they may have on the overall SCADA security. The main task of this paper is to provide a framework that shows how the integration of di®erent state-of-the-art technologies in an energy control system, such as Wireless Sensor Networks (WSNs), Mobile Ad-Hoc Networks (MANETs), and the Internet, can bring some interesting benefits such as status management and anomaly prevention, while maintaining the security of the whole system.